All Articles
The Modern Security Mindset
As remote and hybrid work redefine the modern workplace, traditional VPN security is no longer enough to protect today’s distributed networks. This blog explores the critical differences between VPNs and Zero Trust security, explaining why the old “connect once, trust forever” model leaves organizations vulnerable to lateral movement, credential theft, and insider threats. Learn how Zero Trust architecture uses continuous verification, granular access controls, and device and identity validation to dramatically reduce breach impact. Discover how Tensley Consulting Inc. helps organizations strengthen cybersecurity resilience with modern Zero Trust strategies built for today’s evolving threat landscape.

TechNet Cyber 2026
Event Date: June 2-4, 2026 Attire: Business / Business Casual Location: The Baltimore Convention Center Adversaries have taken to cyberspace to conduct continuous confrontations. Protecting

GITEC 2026
Join federal and industry leaders at CyberScape: The Federal Cybersecurity Summit on April 16, 2026, in Arlington, VA, to explore the latest strategies for addressing evolving cybersecurity threats. Sessions will cover AI, zero trust, identity management, cloud and supply chain security, and protecting critical infrastructure and data.

CyberScape: The Federal Cybersecurity Summit
Join federal and industry leaders at CyberScape: The Federal Cybersecurity Summit on April 16, 2026, in Arlington, VA, to explore the latest strategies for addressing evolving cybersecurity threats. Sessions will cover AI, zero trust, identity management, cloud and supply chain security, and protecting critical infrastructure and data.
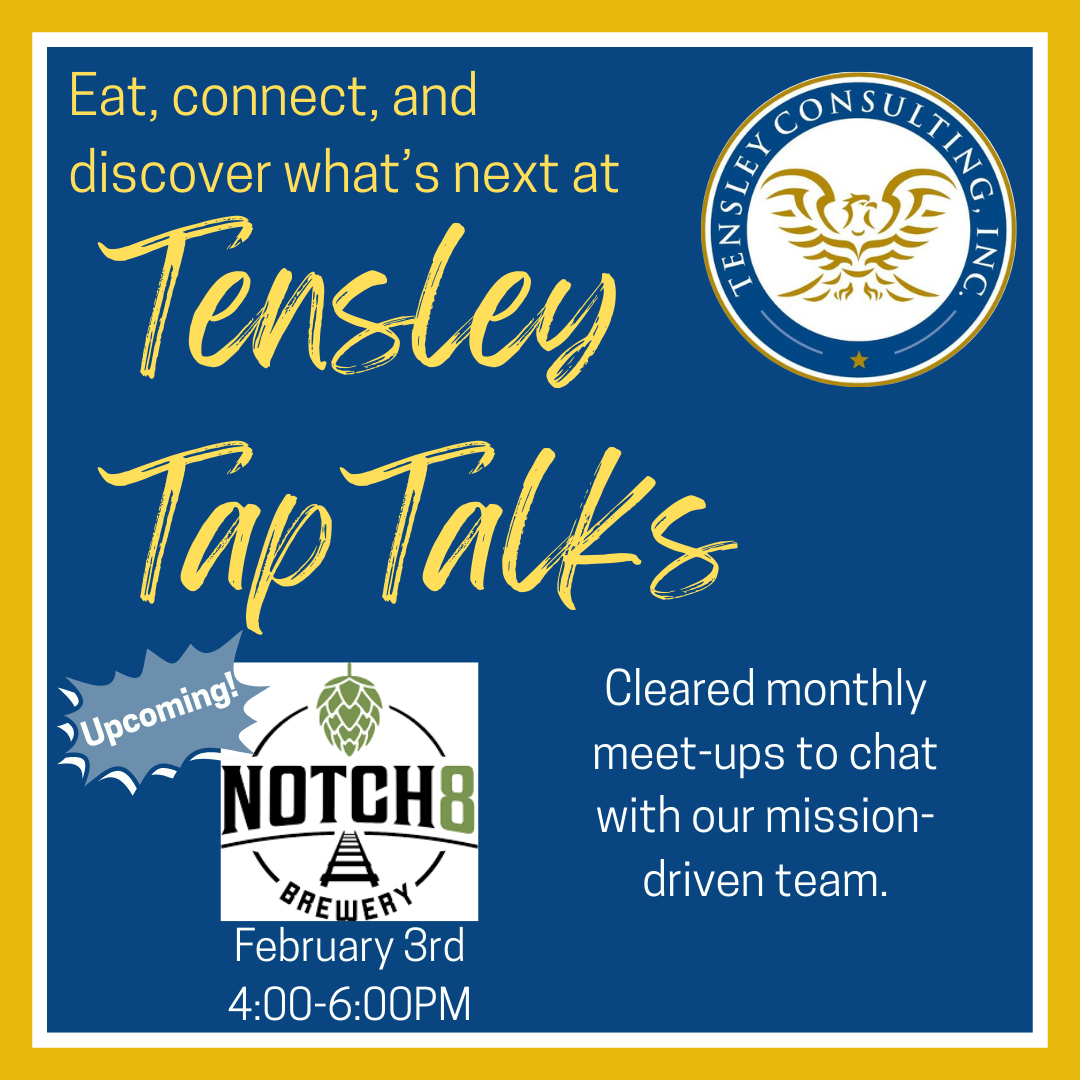
We are back in 2026 for our next Tap Talk!
Join us for an evening of conversation, community, open roles, and mission-driven projects. Pull up a chair and join us for the next Tensley Tap

Tensley Tap Talk at Notch8: Wrapping Up the Year on the Right Track
A year-end Tap Talk full of authentic conversations, new connections, and real insight into Team Tensley’s culture and cleared community.