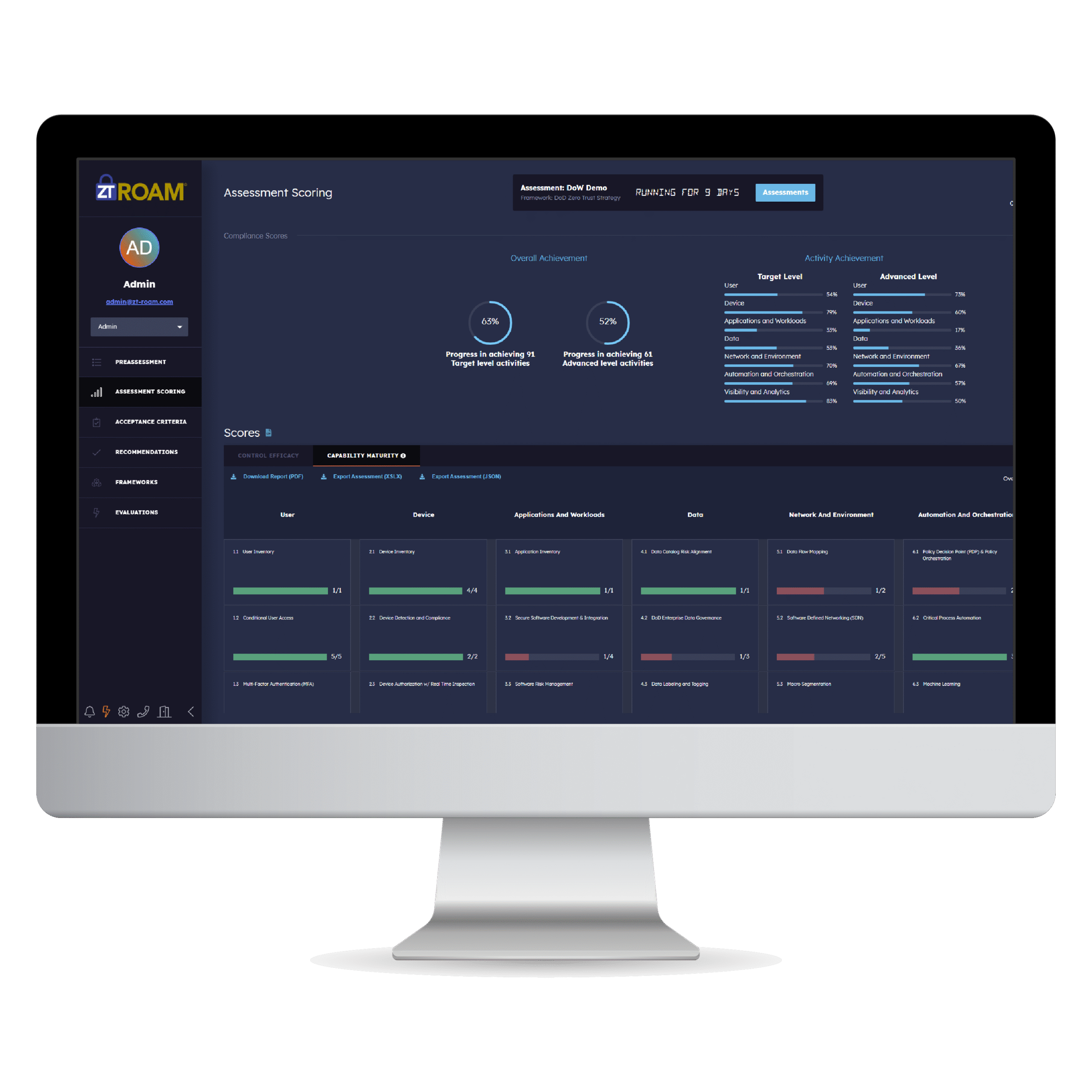
Zero Trust Risk-Based Objective Assessment Methodology (ZT ROAM) Platform
Tensley’s ZT ROAM Platform, developed with our innovative zero trust assessment methodology, empowers your organization with real-time, automated zero trust assessments. Our team has extensive expertise in zero trust and threat-based cybersecurity assessments.
How Do You Know if You Have the Right Security Policies and Capabilities in Place?
History has proven traditional cybersecurity does not work. Aligning to a Zero Trust framework is the solution to protecting your organization and critical data from adversarial threats, but how do you know your policies and capabilities are adequate and correctly configure to achieve the desired outcomes? A Zero Trust assessment with ZTROAM moves your networks to the left of breach.









Zero Trust Compliance In Three Easy Steps.

1. Assess
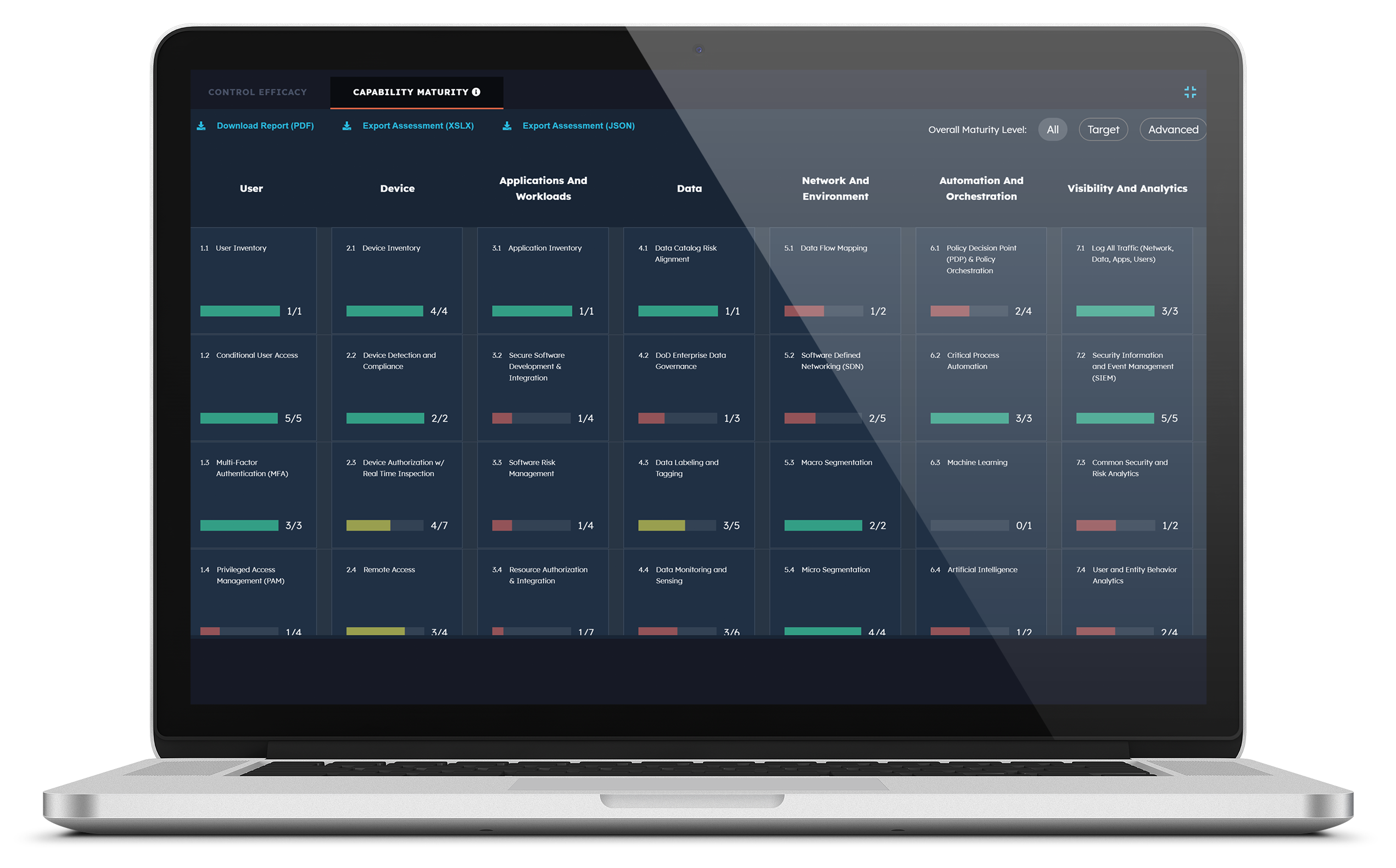
Our Zero Trust assessment tool leverages breach and attack simulation and automated security validation to assess your organization’s level of zero trust maturity and the effectiveness of implemented cybersecurity capabilities and controls.
2. Validate
Our Zero Trust assessment tool validates and visually depicts which zero trust capabilities and activities have been achieved across government and industry frameworks. Your organization’s zero trust capabilities and policies are validated based on our innovative zero trust threat-based assessment methodology.

3. Monitor
Monitor the progress of your Zero Trust transition with our comparison tools and targeted recommendations. Create plans of action and bring your environment into E.O. 14028 Zero Trust compliance.
Who Can Benefit from ZT ROAM?
ZT ROAM’s Integrated Platform is designed to empower a diverse range of industries and professionals. Whether you’re in transportation, logistics, or technology, discover how our innovative solutions can streamline your operations, enhance connectivity, and drive success. Explore the possibilities and see how ZT ROAM can be a game-changer for your business.

Download Our Overview Sheet and Your Guide to ZT ROAM
Discover how the ZT ROAM Integrated Platform can transform your operations with cutting-edge technology and seamless connectivity. Our comprehensive overview provides insights into the features, benefits, and real-world applications of our platform. Fill out the form to download your copy and take the first step toward optimizing your integrated solutions.
Our ZT ROAM Integrated Platform Overview will be delivered right to your email!
Frequently Asked Questions
Transparency matters. Review our complete FAQ page to learn more about ZT Roam’s features, requirements, and policies.
What is ZT ROAM?
Tensley’s ZT ROAM Platform, developed with our innovative zero trust assessment methodology, empowers your organization with real-time, automated zero trust assessments.
Why Zero Trust?
Organizations move to Zero Trust because it dramatically reduces breach risk, protects modern hybrid work environments, and ensures only verified users and devices can access sensitive resources. It replaces outdated perimeter‑based security with continuous verification, making it far harder for attackers to move laterally or exploit implicit trust.
Can ZT ROAM export assessment results?
Yes, executive summaries, assessment results, and recommendations can be exported in three formats: PDF, XSLX, and JSON.
What is the cost of a license for ZT ROAM?
…
Where can I download the software?
Licensing and software are available on our ZT ROAM download portal.
Does ZT ROAM or Tensley keep my data?
No, you are in complete control of software user access as well as the assessment data. We are an agentless platform.
Is ZT ROAM training available?
Yes, training and professional services are available for users of ZT ROAM.
Can I perform manual assessments with ZT ROAM?
Can I perform manual assessments with ZT ROAM?
What are the ZT ROAM OS requirements?
RHEL 9 or Rocky Linux 9
Docker – v20.10.22+
Docker-compose – v2.14.1+
What are the ZT ROAM hardware requirements?
-Processor – 64-bit x86 CPU with at least 4 cores
-Memory – 16GB
-Disk Storage – 200GB
-Disk Type – 10k SAS+
-Network – Single network interface; Static Routable IP addresses required
What are the ZT ROAM Network Requirements?
ZTROAM needs permissions to create and run Docker containers via Docker Compose.
Port 443: Inbound / ZT ROAM UI
Port 8089: Outbound / SIEM (Optional)
Port 443: Outbound / BAS or Security Tool (Optional)
Is ZT ROAM’s data encrypted?
Passwords and Data at Rest are encrypted within ZT ROAM.
Latest News
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Ut elit tellus, luctus nec ullamcorper mattis, pulvinar dapibus leo.
The Modern Security Mindset
As remote and hybrid work redefine the modern workplace, traditional VPN security is no longer enough to protect today’s distributed networks. This blog explores the critical differences between VPNs and Zero Trust security, explaining why the old “connect once, trust forever” model leaves organizations vulnerable to lateral movement, credential theft, and insider threats. Learn how Zero Trust architecture uses continuous verification, granular access controls, and device and identity validation to dramatically reduce breach impact. Discover how Tensley Consulting Inc. helps organizations strengthen cybersecurity resilience with modern Zero Trust strategies built for today’s evolving threat landscape.
GITEC 2026
Join federal and industry leaders at CyberScape: The Federal Cybersecurity Summit on April 16, 2026, in Arlington, VA, to explore the latest strategies for addressing evolving cybersecurity threats. Sessions will cover AI, zero trust, identity management, cloud and supply chain security, and protecting critical infrastructure and data.
ZT ROAM Elevates Your Organization’s Cybersecurity
Automated Security Validation
Leverage Breach and attack simulation and automated security validation with latest intelligence. Mapped to the MITRE ATT&CK adversary lifecycle framework.
Continuous Zero Trust Assessments
Continually assess and validate zero trust policies with automated threat-based cybersecurity.
Flexible Zero Trust Assessments
Evaluate your organization’s level of zero trust maturity and cybersecurity based on your needs, such as one-time, quarterly or annually.
Zero Trust Optimization
Automatically identifies zero trust gaps to support delivering zero trust maturity recommendations.
Start Strengthening Your Zero Trust Strategy
Have questions? Want to discuss your environment?
Tensley Consulting helps commercial organizations move beyond check-the-box compliance and toward measurable, continuous Zero Trust security validation.